Protecting sensitive HR data is non-negotiable. Encryption within your Applicant Tracking System (ATS) ensures candidate and employee information, like Social Security numbers and financial records, stays secure. Here’s what you need to know:
- Encryption Basics: Convert sensitive data into unreadable formats using AES-256 for stored data and TLS 1.2+ for transmitted data.
- Regulatory Compliance: Laws like GDPR, CCPA, and HIPAA often require encryption to avoid severe penalties.
- Key Practices:
- Encrypt both stored and transmitted data.
- Use role-based access controls (RBAC) to limit who can view sensitive information.
- Apply regular updates and security patches to your ATS.
- Train HR teams on security protocols.
- Maintain detailed audit logs for compliance and breach detection.
Skillfuel, a leading ATS platform, automates encryption, access controls, and compliance tracking, simplifying security management for HR teams.
Encryption isn’t just about compliance – it’s about earning trust and protecting your organization’s reputation.
Encrypting Data at Rest and Transit – How to Protect Your Data
Basic Encryption Practices for ATS Security
In addition to adhering to regulatory requirements, implementing strong encryption practices is a key step in securing your Applicant Tracking System (ATS).
Encryption Methods: At-Rest and In-Transit
When it comes to protecting your ATS, encryption can be broken down into two main categories: data at rest and data in transit.
- Data at rest refers to information stored in places like databases, servers, or backups. Think of candidate profiles, resumes, and interview notes. Protecting this data typically involves using advanced algorithms, such as AES-256, to ensure that even if someone gains unauthorized access, the information remains unreadable.
- Data in transit, on the other hand, includes information being transmitted across networks. Examples include when a candidate submits their application or when HR staff access records remotely. To secure this data, protocols like TLS (Transport Layer Security) are used to create encrypted communication channels.
Both forms of encryption work together to provide a strong defense against breaches, ensuring sensitive ATS data is protected at all stages.
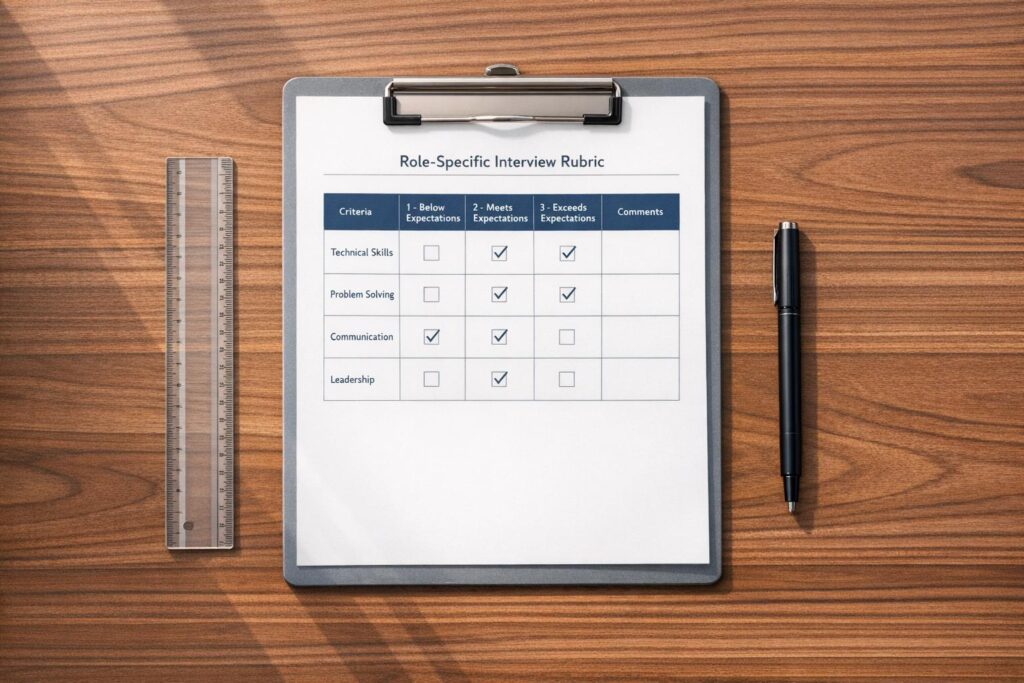
Role-Based Access Control (RBAC)
Encryption is only part of the equation. Role-based access control (RBAC) ensures that sensitive information is accessible only to those who need it for their job. By assigning specific access levels based on roles, you reduce the chances of unauthorized personnel viewing confidential data.
For instance, a recruiting coordinator might only need access to basic candidate details like contact information and interview schedules. Meanwhile, senior HR managers could access more sensitive data, such as salary discussions or background check results. This layered approach is especially critical when handling highly sensitive details, such as Social Security numbers or medical accommodations. Clearly defining access levels for each role safeguards your ATS from internal misuse.
Regular Updates and Security Patches
Even the strongest encryption can falter if your software is outdated. Hackers often exploit vulnerabilities in older systems, making regular updates and security patches essential for staying one step ahead of cyber threats.
Security patches are designed to fix weaknesses discovered in previous versions of software, effectively closing loopholes that attackers might exploit. Delays in applying these patches can leave your ATS exposed to known vulnerabilities. To prevent this, establish a routine update schedule and prioritize critical patches. This should extend not only to your ATS software but also to operating systems, databases, and any supporting network infrastructure.
Automated update notifications and thorough testing procedures can help ensure patches are applied quickly without disrupting your hiring processes. These proactive measures build a solid foundation for keeping your ATS secure and ready for future challenges.
ATS Data Encryption Checklist for HR Teams
Follow these steps to strengthen encryption and access controls within your Applicant Tracking System (ATS).
Check Encryption Protocols
Ensure your ATS uses AES-256 encryption for data at rest and TLS 1.2 or higher for data in transit. This applies to both the database and backups. Double-check that these protocols are active and properly configured.
Make sure all candidate data – like resumes, personal details, and interview notes – are encrypted in your database. Backups should follow the same encryption standards. If your system doesn’t meet these requirements, upgrading should be a top priority to align with current security practices.
Keep encryption keys stored separately from the data itself, and rotate them regularly according to your organization’s security policies. This separation ensures that even if encrypted data is accessed, it cannot be decrypted without the appropriate keys.
Review Access Control Policies
Perform quarterly audits of user permissions. Revoke access immediately when employees change roles or leave the company. Enforce multi-factor authentication (MFA) for all users, especially administrators, and consider requiring MFA for any remote system access.
Maintain a detailed record of who has access to specific data and the reasons for it. Implement a clear approval process for granting new permissions, requiring manager authorization for any changes. This documentation will be essential during security audits and compliance checks.
Run Regular Security Audits
Schedule monthly vulnerability scans and quarterly penetration tests to identify and address security gaps. Use automated alerts to monitor system logs for unusual activity, such as multiple failed login attempts or unauthorized access attempts. Collaborate with your IT security team or external consultants to ensure a thorough review.
Test your backup and recovery procedures during each audit cycle. Confirm that encrypted backups can be restored successfully without compromising data security. Document the time it takes to recover your system fully; this information is critical for business continuity planning.
Train HR Teams on Security Practices
Provide mandatory security training twice a year. Cover topics like creating strong passwords, recognizing phishing attempts, securely managing candidate data, and responding to potential security incidents. Ensure all team members understand their role in safeguarding sensitive information.
Develop clear protocols for handling candidate data outside the ATS, such as printing resumes or sharing information via email. Set guidelines for secure communication with candidates and hiring managers, including when to use encrypted email for sensitive details.
Document Encryption Standards
Keep a detailed record of your encryption protocols, access control policies, and security procedures. This documentation should be clear enough for new team members to understand and follow.
Create a security policy handbook that outlines data classification, encryption requirements, and compliance obligations. Include step-by-step procedures for handling different types of candidate data, from basic contact details to sensitive background checks. Use version control to keep the handbook up-to-date and ready for audits. Proper documentation also ensures compliance with regulations such as GDPR, CCPA, and HIPAA.
sbb-itb-e5b9d13
Compliance and Audit Requirements for HR Teams
Navigating legal standards and preparing for data audits demands careful and organized documentation. One key element in this process is maintaining detailed audit trails.
Keep Audit Trails
Audit trails are your first line of defense against data breaches and a critical tool for meeting compliance standards. These records, which are time-stamped, log every interaction with candidate and employee data – capturing details like the user involved, the exact timestamp, and the action taken. Considering that insider threats are responsible for nearly 60% of data breaches, having a robust audit trail system is non-negotiable for safeguarding sensitive HR information.
Your applicant tracking system (ATS) should be set up to log every interaction with data. This includes actions like uploading resumes, editing documents, making role changes, and updating permissions. It’s also crucial to configure the system to track any updates to permissions or access settings across all user accounts.
To stay ahead of potential threats, implement automated alerts for unusual access patterns. Regularly review logs to spot anomalies, such as repeated failed login attempts or unauthorized permission changes. These alerts allow your team to respond quickly to potential security issues. For compliance with SOX external audit requirements, retain at least 366 days of audit logs.
Finally, document any irregularities thoroughly for further investigation. These practices not only support compliance but also strengthen your response to potential security incidents.
Skillfuel‘s Encryption Features and Benefits
Skillfuel takes ATS encryption to the next level, offering security features tailored specifically for HR needs. Its platform addresses common HR security challenges with automated encryption and compliance tools that simplify the recruitment process.
Skillfuel’s Centralized Security Management
Skillfuel provides HR teams with a centralized dashboard that serves as a single control hub for all security-related functions in the recruitment process. This streamlined approach ensures that every aspect of security is managed efficiently and effectively.
The platform also automates GDPR compliance by tracking candidate consent and monitoring data processing activities. This eliminates the need for manual oversight, making it easier to meet regulatory requirements.
Customizable access controls allow precise role-based permissions, giving you the ability to restrict access to sensitive information. For example, you can limit who can view salary expectations, access specific candidate pools, or modify records. These tailored permissions ensure that team members only interact with the data necessary for their roles, reducing risks.
Another standout feature is the encryption of candidate communications, which is especially critical for high-volume recruitment. Every communication is logged and encrypted, creating a secure audit trail. This ensures sensitive information remains protected throughout the entire candidate lifecycle, from first contact to final hire.
Skillfuel’s centralized controls integrate seamlessly with its automated compliance tools, making it easier to maintain security across your recruitment workflows.
Simplify Compliance with Skillfuel
Skillfuel’s compliance tools turn traditionally tedious manual processes into automated, behind-the-scenes operations. Every interaction with candidate data is automatically logged, complete with timestamps and user actions. These detailed records complement the platform’s access controls, offering an extra layer of transparency and security.
By using a centralized candidate repository, Skillfuel ensures all sensitive data stays within one secure environment. This eliminates the risks associated with scattered data across multiple systems or devices. Centralization not only improves data protection but also provides better visibility into how information moves through your recruitment process.
Features like real-time calendar sync and Kanban workflow management maintain security at every stage of hiring. Whether candidates are in the screening phase, interview scheduling, or final decision-making, each transition is logged and secured. This ensures that data protection standards remain consistent, no matter where candidates are in the hiring pipeline.
Skillfuel’s encryption and compliance tools offer HR teams a reliable way to secure sensitive information while simplifying day-to-day operations.
Key Takeaways for HR Teams
Data encryption within your ATS isn’t just a technical necessity – it’s a cornerstone of trust between your organization and candidates. Safeguarding sensitive details like Social Security numbers, salary expectations, and personal communications directly influences your company’s reputation and legal compliance.
The most important encryption practices revolve around securing data at rest and in transit. This means protecting stored information as well as data being transmitted, ensuring comprehensive security. Adding role-based access controls ensures that only authorized team members can access specific candidate information, significantly reducing the risk of internal breaches.
Beyond encryption, regular security audits and ongoing team training are crucial. Even the most advanced security measures are only as effective as the people implementing them. HR teams should stay informed about phishing threats, password best practices, and proper data handling to maintain recruitment system integrity.
Compliance with regulations like GDPR and CCPA requires detailed audit trails and clear records of consent. A well-documented data breach response plan is another must-have, helping organizations minimize damage and meet legal notification deadlines if an incident occurs.
Skillfuel simplifies these challenges with its centralized security management tools. By automating many time-consuming tasks, these tools make ATS security easier to manage. This allows HR teams to focus on what matters most – finding the right candidates – while ensuring top-tier data protection.
Strong ATS encryption doesn’t just protect data; it reduces legal risks, builds candidate trust, and simplifies compliance. Companies that prioritize security from the outset avoid the financial and reputational fallout of breaches and regulatory violations, setting themselves up for long-term success.
FAQs
What risks does an ATS face without data encryption, and how does encryption help protect sensitive information?
When an Applicant Tracking System (ATS) lacks data encryption, it opens the door to major risks like data breaches, identity theft, and financial fraud. These threats can result in legal troubles, damage to your reputation, and hefty financial setbacks for your organization.
Encryption serves as a shield for sensitive information, transforming it into a format that’s unreadable to anyone without proper authorization. Even if someone manages to access the data illegally, encryption keeps it secure. This not only helps your organization stay in line with data protection laws but also reduces the potential fallout from breaches.
How does Skillfuel help HR teams comply with data privacy regulations like GDPR and CCPA?
Skillfuel makes navigating data privacy regulations like GDPR and CCPA much easier by providing a centralized platform for security management. With everything in one place, HR teams can efficiently oversee security controls and track audit trails, simplifying the task of enforcing data protection policies.
By keeping security measures consistent and logging every instance of data access and handling, Skillfuel promotes both transparency and accountability. This reduces the chances of non-compliance and streamlines the process of proving regulatory adherence during audits, helping to avoid costly penalties.
Why is role-based access control (RBAC) essential for protecting sensitive HR data, and how does it work with encryption?
Role-based access control (RBAC) plays a critical role in safeguarding sensitive HR data by ensuring employees can only access the information necessary for their specific job duties. This approach reduces the chances of unauthorized access, accidental data exposure, or misuse by tailoring permissions to each role within the organization.
RBAC complements encryption to create a stronger security framework. Encryption secures data by rendering it unreadable without the correct decryption key, while RBAC ensures that only authorized individuals can access those keys or view the decrypted information. Together, these measures provide a robust defense against potential breaches or leaks.